Japanese auto major Toyota Motor Corp. is recalling around 1 million vehicles under Toyota and Lexus brands in the United...
Is the Securities and Exchange Commission (SEC) set to approve the first “spot” Bitcoin exchange-traded fund (ETF) by January 10,...
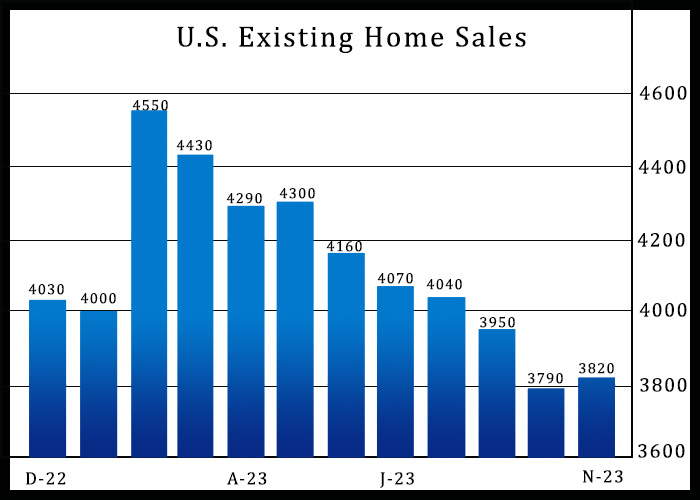
After reporting five consecutive monthly declines in U.S. existing home sales, the National Association of Realtors released a report on Wednesday showing existing home sales unexpectedly rebounded in the month...
Florida school is slammed for forcing a TWO-year-old black girl to take part in a Rosa Parks reenactment that involved white toddler 'handcuffing her and taking her fingerprints' Building Brains...
Wallbox N.V. (WBX), a charging solutions provider, announced on Wednesday...
As the total market capitalization of the cryptocurrency space keeps...